Access control credentials are often seen as a simple component of a security system — a card, a fob, or a mobile app used to unlock doors.
In reality, credentials are one of the most critical design elements in any access control system.
The way credentials are defined, assigned, and managed has a direct impact on:
- security effectiveness
- system scalability
- administrative workload
- long-term operational efficiency
For organizations planning or reviewing a system, understanding credential strategy early can prevent costly issues later.
What Is an Access Control Credential?
An access control credential is not just a physical object.
It represents:
a person’s identity and their permissions within a system
A credential links:
- a user (employee, contractor, visitor)
- to specific access rights (doors, schedules, zones)
Whether it is:
- a badge
- a key fob
- a mobile credential
- or a biometric identifier
…the function remains the same: identify and authorize access.
Types of Access Control Credentials
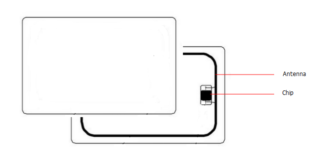
1. Card-Based Credentials (RFID)
The most common option in commercial environments.
Advantages:
- cost-effective
- easy to deploy
- widely supported
Limitations:
- can be lost or shared
- cloning risks depending on technology
2. Key Fobs
Similar to cards but more compact.
Often used for:
- convenience
- quick access environments
3. Mobile Credentials
Credentials stored on a smartphone using technologies like NFC or Bluetooth.
Advantages:
- reduced need for physical cards
- harder to share unintentionally
- can be managed remotely
Considerations:
- device compatibility
- user adoption
- system integration
4. Biometric Credentials
Fingerprint, facial recognition, or other biological identifiers.
Advantages:
- tied directly to the individual
- cannot be forgotten or shared
Considerations:
- privacy concerns
- environmental limitations
- higher cost
Why Credential Strategy Matters More Than Technology
Many systems fail not because of hardware limitations, but because of poor credential planning.
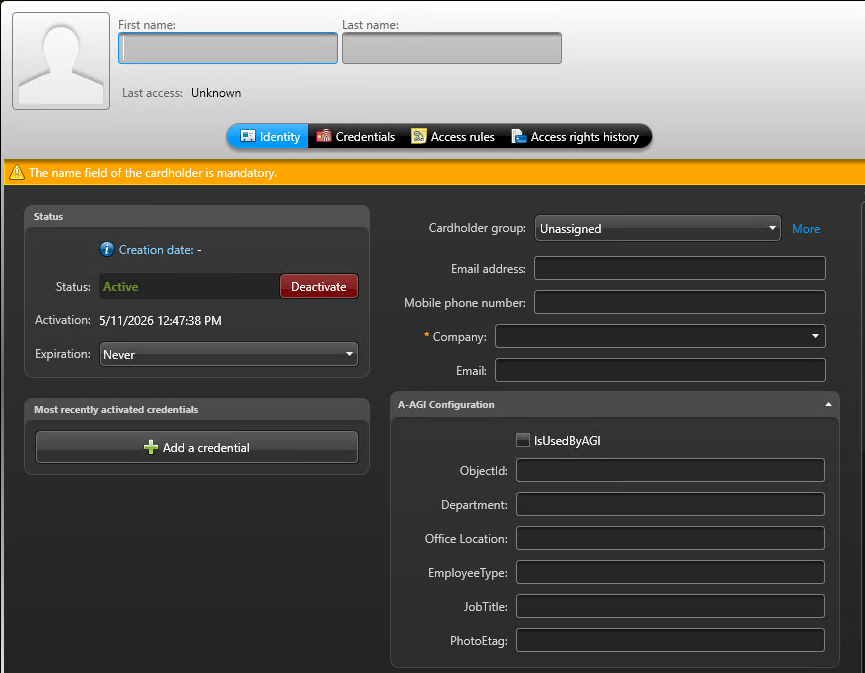
🔑 1. Credentials Define Identity Structure
Credentials are the foundation of:
- user organization
- access groups
- system logic
If identities are not structured properly:
- permissions become inconsistent
- administration becomes complex
- errors increase over time
⚠️ 2. Common Mistakes in Credential Management
Treating credentials as “just badges”
Without linking them to a structured identity model.
No naming or organizational convention
Making it difficult to track users and permissions.
Mixing credential types without planning
Creating inconsistency across the system.
Lack of lifecycle management
Old credentials remain active, increasing risk
🧱 3. Impact on System Scalability
As organizations grow:
- more users
- more doors
- more locations
A poorly structured credential system leads to:
- duplication of effort
- complex access rules
- increased administrative time
In platforms like Genetec Security Center, this often becomes visible when systems expand across multiple sites.
To understand how credentials fit into a full system design, you can also read:
👉 Genetec Security Center Architecture and System Structure
🔄 4. Credential Lifecycle Management
A well-designed system considers the full lifecycle:
Onboarding
- creating credentials
- assigning access
Changes
- role updates
- department transfers
Offboarding
- revoking access immediately
Without clear processes, systems accumulate:
- inactive users
- unnecessary security risks
Real-World Insight: Where Systems Go Wrong
In many commercial environments, issues don’t appear immediately.
They develop over time:
- inconsistent user setup
- duplicated credentials
- unclear access rights
- difficulty auditing permissions
These problems are rarely caused by technology.
They are usually the result of:
early decisions made without a clear credential strategy
What Decision-Makers Should Consider
Before implementing or upgrading a system, ask:
- How are identities structured in the system?
- Are credential types standardized?
- How will access be managed as the organization grows?
- What processes exist for onboarding and offboarding?
- Can the system be easily audited?
These questions are often more important than:
- brand selection
- hardware specifications
Key Takeaway
Access control credentials are not just tools for opening doors.
They are:
the foundation of how a security system understands and manages people
A well-planned credential strategy leads to:
- simpler administration
- better security
- long-term scalability
A poorly planned one creates complexity that grows over time.
Final Thought
Organizations often focus on readers, controllers, and software platforms.
But in practice:
credential strategy is one of the most important decisions in access control design
Taking the time to define it properly early can prevent significant operational challenges later.